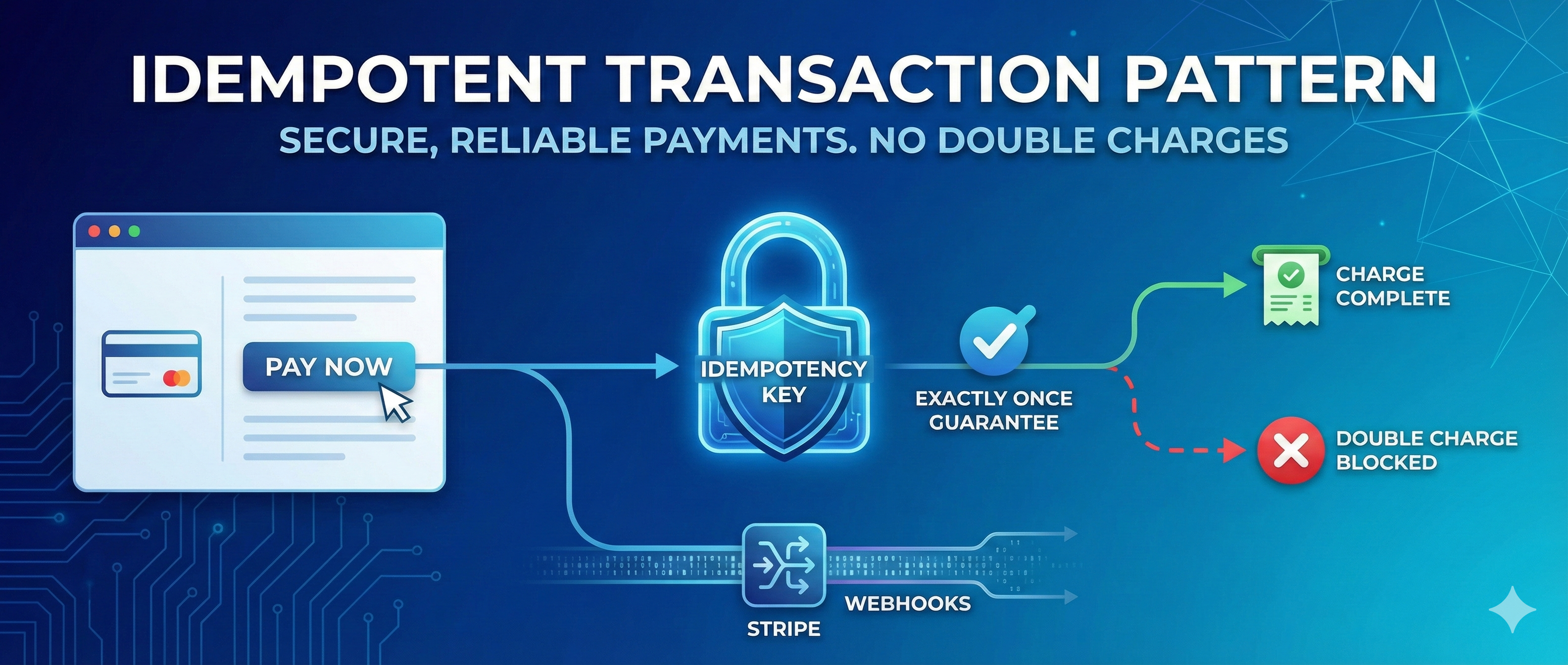
Secure Payment API Integration: Idempotency & Webhooks
A critical look at building robust payment flows using Stripe. Handling race conditions, ensuring idempotency, and securing webhook endpoints.
Project Overview
Integrating a payment gateway like Stripe looks easy on the surface, but edge cases abound. Network timeouts, double-clicks, and delayed webhooks can lead to double charges or missed access provisioning. This guide details our 'Idempotent Transaction Pattern' which guarantees that every payment action happens exactly once, regardless of network failures.
System Architecture
The payment flow involves three parties: Content (User), Server (API), and Gateway (Stripe). Our server creates a PaymentIntent and passes a client_secret to the frontend. Crucially, we use Idempotency Keys for all write operations to Stripe. Fulfillment happens asynchronously via Webhooks, verified by cryptographic signatures to prevent spoofing.
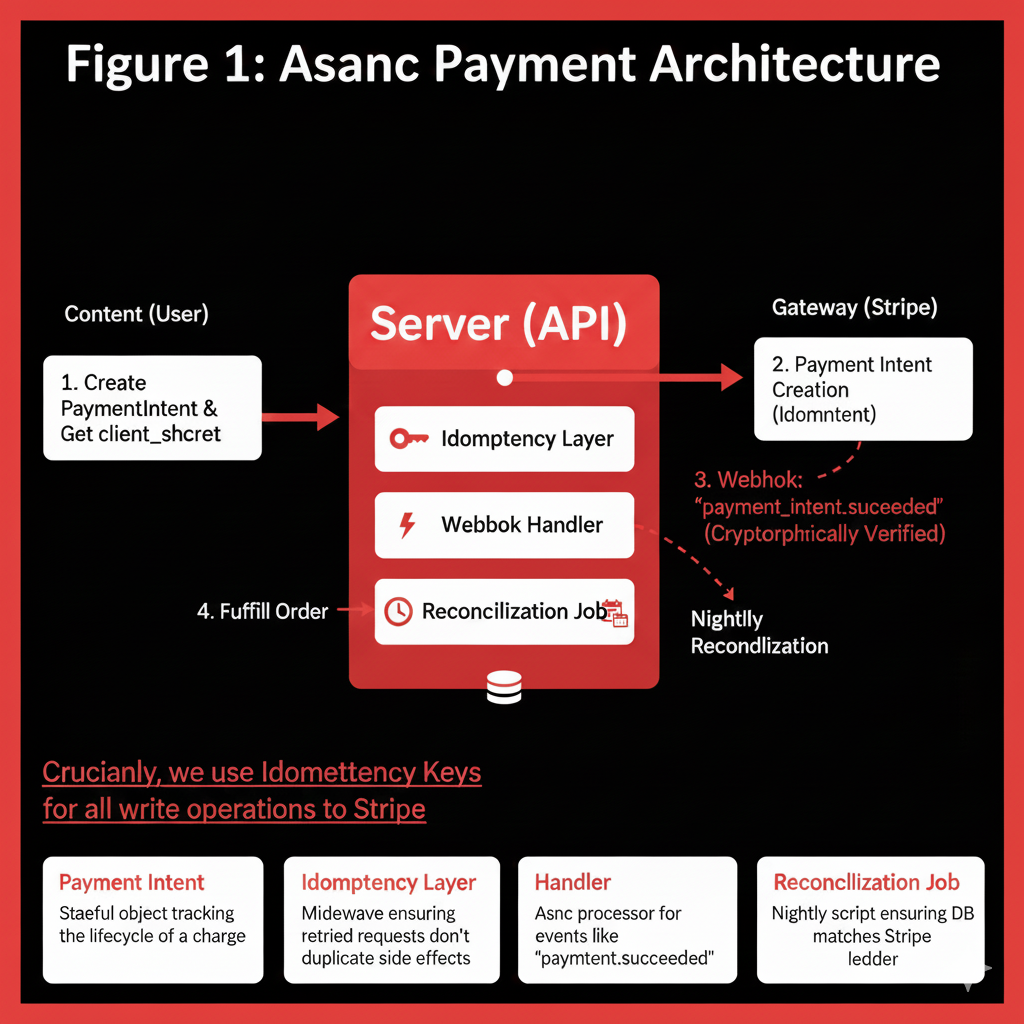
Payment Intent
Stateful object tracking the lifecycle of a charge.
Idempotency Layer
Middleware ensuring retried requests don't duplicate side effects.
Webhook Handler
Async processor for events like 'payment_intent.succeeded'.
Reconciliation Job
Nightly script ensuring DB matches Stripe ledger.
Implementation Details
Code Example
@app.post("/webhook")\nasync def stripe_webhook(request: Request):\n payload = await request.body()\n sig_header = request.headers.get('Stripe-Signature')\n try:\n event = stripe.Webhook.construct_event(\n payload, sig_header, webhook_secret\n )\n except ValueError:\n raise HTTPException(400)\n \n if event['type'] == 'checkout.session.completed':\n await provision_access(event['data']['object'])\n return {"status": "success"}Agent Memory
Always pass `idempotency_key` (e.g., a UUID) in Stripe API calls. If the network drops the response, you can safely retry the exact same call, and Stripe knows to return the cached result instead of charging again.
Workflow
Cart Checkout: User initiates payment.\n2. Intent Creation: Server creates generic PaymentIntent with Metadata.\n3. Processing: Stripe securely collects card details.\n4. Confirmation: Stripe signals success via Webhook.\n5. Fulfillment: Server verifies signature and grants product access.

Results & Impact
" Implementing strict webhooks and idempotency saved us from hundreds of support tickets regarding duplicate charge disputes."
Trust
Users feel secure knowing billing is accurate.
Compliance
Fully audit-ready transaction logs.
Resilience
Immune to frontend connectivity drops.
About the Author
Rahul Patil
AI Context Engineer
Apex Neural
Rahul engineers context-aware AI systems that improve model reliability and decision quality. He focuses on RAG pipelines, structured prompt flows, and multi-agent orchestration to ensure AI systems are grounded, secure, and production-ready.
Ready to Build Your AI Solution?
Get a free consultation and see how we can help transform your business.
